In an increasingly interconnected world, the task of keeping your digital life in order while protecting your personal privacy has never been more critical. With data breaches, identity theft, and surveillance on the rise, taking time to clean up your digital footprint is not just an act of organization—it’s a step toward digital resilience. Fortunately, by approaching this task systematically, you can reduce clutter while safeguarding your sensitive information.
1. Start With a Digital Inventory
The first step to tidying your digital life is understanding what you have. Most of us accumulate files, apps, and accounts over time that we no longer use or need.
- Emails: Go through your inbox and delete old messages, especially those with personal data or financial details.
- Cloud Storage: Review your files in services such as Google Drive or Dropbox, and delete duplicates or irrelevant content.
- Devices: Audit your laptops, smartphones, and tablets for rarely used apps or stored media that can be safely deleted.
Establish a schedule to periodically revisit this inventory so that it doesn’t become unmanageable in the future.
2. Delete Unused Online Accounts
Every account you create is a potential vulnerability. Sites you signed up for years ago might no longer have strong security, but can still store valuable information about you.
Use tools like JustDeleteMe or simply search “how to delete [website] account” to begin the cleanup process. If you’ve previously reused passwords across websites, delete those accounts—and update your credentials more broadly for better defense against credential stuffing attacks.
3. Strengthen Your Passwords
Weak or reused passwords are a leading cause of data breaches. Take time to update your login credentials using these guidelines:
- Use a self hosted password manager: Tools like Bitwarden, 1Password, or LastPass can securely store and generate strong, unique passwords.
- Enable multi-factor authentication (MFA): Where available, enable MFA for sensitive accounts such as banking, email, or social platforms.
- Avoid patterns: Don’t rely on birthdays or pet names that can be guessed through social engineering.
4. Review App Permissions
Over time, your phone and web applications accumulate permissions that may overreach their necessities. For example, a flashlight app doesn’t need access to your contacts or location. Regularly reassess this through your phone’s settings.
On Android, go to Settings > Apps > Permissions. On iOS, it’s Settings > Privacy. Revoke any non-essential access to reduce data leakage risks.

5. Clean Your Social Media Presence
Old tweets, Facebook posts, or Instagram photos can paint an outdated or unflattering picture. Worse, personal content can be harvested or used against you.
- Perform a content audit: Use built-in tools or services like TweetDelete or Jumbo Privacy to remove or archive old posts.
- Change visibility settings: Make old posts private or restrict access to trusted circles only.
- Control tagging: Disable automatic tagging or require your approval on posts you’re tagged in.
Also consider what personal data is visible to the public, such as contact info, job history, or family relationships. Sharing less reduces your exposure.
6. Secure Your Devices
Your digital work means little if your hardware is vulnerable. To tighten device security:
- Apply regular software updates: This includes operating systems, browsers, and apps. Security patches are often bundled in updates.
- Use antivirus and firewall utilities: Reputable tools provide a strong first line of defense against online threats.
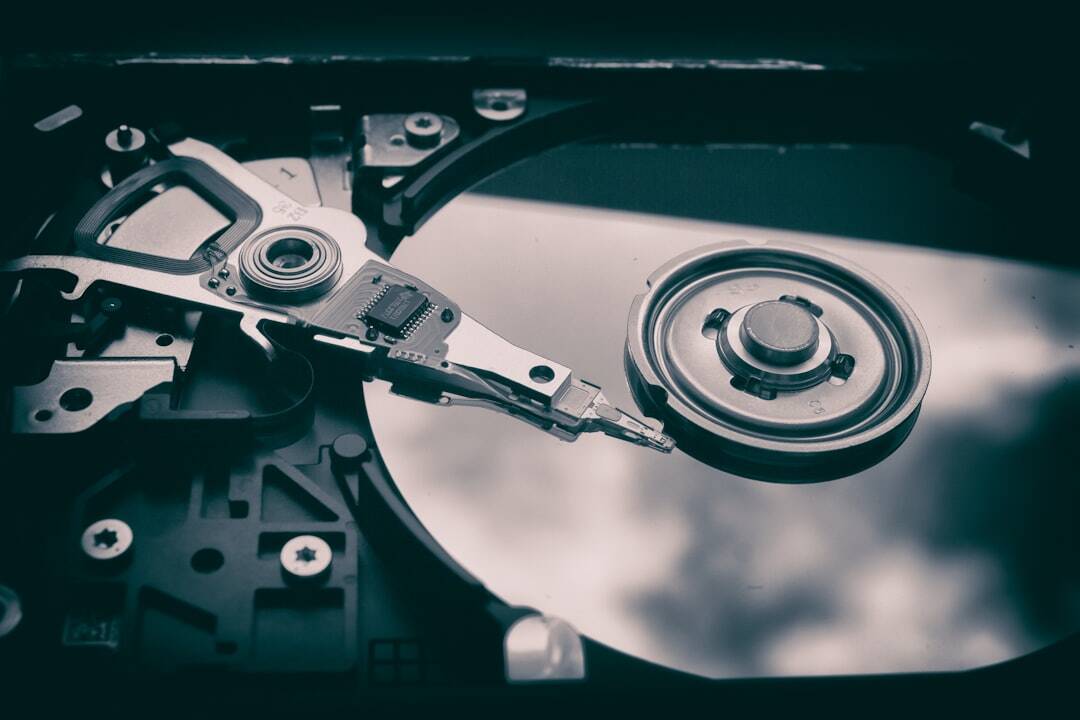
- Encrypt your devices: Enable full-disk encryption, especially on laptops and mobile phones that might be lost or stolen.
7. Back Up Important Data
Deleting and organizing documents is fine, but make sure you have backups of irreplaceable data before any major cleanup. Use the 3-2-1 backup method:
- Three total copies of your data
- Two stored locally (on separate devices)
- One stored off-site (such as secure cloud storage)
This method protects you not only from accidental deletion but also from cyberattacks like ransomware.
8. Read Privacy Policies (Yes, Really)
Before signing up for new services or apps, spend a few minutes reviewing their privacy policies. While tedious, these documents can reveal if your data will be sold to third parties, where it’s stored, or how you can delete it later.
Look for red flags like:
- Data collection for advertising purposes
- Sharing data with “partners” with unclear identities
- Lack of account deletion options
Conclusion
Tidying up your digital life is more than just deleting old files or clearing your inbox. It is a comprehensive process that boosts both digital efficiency and personal security. By taking a proactive and vigilant approach, you not only gain peace of mind but also reduce your exposure to ever-evolving privacy threats. Make this effort a regular habit—and consider it an investment in your digital future.